Audit Services
Access Control Review
The security of your organization’s data is important. To make it secure, you need to be aware of the activities performed with the data. The data should be accessible to people who have certain privileges. Otherwise, in the event of any loss or damage, you will be unable to identify the reason that any unauthorized user has wrongfully used their rights to access data.
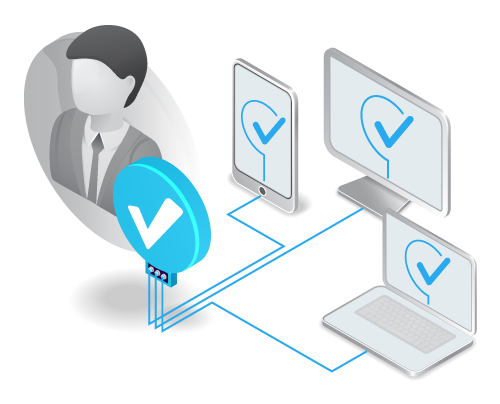
Access control is a technique to limit the access of resources or information to certain people, for security purpose. For computer security, organizations implement access control to ensure that each entity trying to access resources possess certain rights and permission. In computer systems, there is an access control list which includes the list of permissions required by particular user to access the data. It helps to secure data and define privileges as to regulate who or what can view the information.
Objective of This Assessment
User access review uses a principle of ‘least privileges’. A user access review helps you in monitoring the appropriateness of an entity to view or update the information. A user should be given access to only those resources which are necessary to perform their tasks, while preventing the access to resources which are irrelevant to the user.
The access control method involves three phases to mitigate security risks of information. The three phases are as follows:
Related Audit Services
Approach & Methodology
An organization should have a template of a written standard of access control review. It would serve as a guide for security analysts and other people associated with information security. The overview is as follows:
It is recommended that you should select an access control system which has a robust management interface. Access control review is easier to be performed afterwards.



